
JOBS POLICIES, ANALYSIS, AND RESOURCES
Latest Jobs Posts
2026 Democratic Primary Preview Series: Minnesota
Minnesota has emerged as a central battleground in the broader political and cultural conflicts shaping the country in recent years. From the police killing of George Floyd in 2020 to renewed clashes over federal immigration enforcement and ICE activity, the state, particularly the Twin Cities, has become a focal point for activism, protest, and national political attention. These developments have helped shape both voter engagement and partisan dynamics heading into the 2026 election cycle.
2026 Democratic Primary Preview Series: Massachusetts
Massachusetts, or the Bay State, is a safe state for Democrats in 2026. While the state has a wonky history of electing a Republican Governor, all three major seats are held by Democrats- this includes the Governorship & the two Senate seats held by Elizabeth Warren & Ed Markey, who are both in their 13th year in their respective seats. Moving down the ballot, the remaining congressional breakdown is 9-0 in Democrats’ favor, with 8 of the 9 incumbents running for re-election. The primary elections are set for September 9th, followed by the general election on November 3.
Flying Blind — The Economic Sabotage of the Federal Shutdown (Economic Policy Brief #92)
While the full federal government reopened in early 2026, the United States remains in a state of economic volatility due to a lingering partial shutdown of the Department of Homeland Security (DHS), now entering its 67th day.
Generational Change
Op Ed | Ron Israel | Managing Editor, USRESIST NEWS | April 19, 2026 Look at the evolution of life in America over the last several generations. I did this recently after my daughter came and asked me how she would be able to live well during her later years, when...
Grindr Hosts Networking Event Ahead of WH Correspondents’ Dinner to Advocate for LGBT Policy Change (Social Justice Policy Brief #190)
LGBT hookup app, Grindr, will host its inaugural White House Correspondents’ Dinner Weekend Party on April 24, one day before the White House Correspondents’ Dinner.
The Week That Was: Global News in Review (Foreign Policy Brief #232)
Iran has vowed retaliation after a US destroyer fired on an Iranian-flagged cargo ship in the Gulf of Oman late last week.
Professional Exclusion and the Texas Workforce Crisis
Between March 29 and April 6, 2026, a major workforce crisis intensified across Texas as state regulatory bodies began a coordinated effort to revoke or deny occupational licenses for non-citizens and DACA (Deferred Action for Childhood Arrivals) recipients.
Issues Affecting Democrat Messaging in the Upcoming Midterm Elections (Elections and Politics Brief #204)
With the 2026 midterm general elections approaching, analytics show Democrats rebuilding national attention. Though it is early, special election results, voter enthusiasm and new candidates suggest what some analysts call a possible Democratic “blue wave.”
2026 Democratic Primary Preview Series: New York
New York often sits in the average voter’s mind as a solid blue state, almost as a homogenous Democrat stronghold. With the recent election of Zohran Mamdani as the mayor of NYC, one wouldn’t be faulted for assuming that the rest of the state is skewed towards the left to some degree. Representatives like Alexandria Ocasio-Cortez, House Minority Leader Hakeem Jeffries, and Senate Minority Leader Chuck Schumer lend credence to this impression.


2026 Democratic Primary Preview Series: Massachusetts
2026 Democratic Primary Preview Series | Morgan Davidson
3/29/2026
Massachusetts, or the Bay State, is a safe state for Democrats in 2026. While the state has a wonky history of electing a Republican Governor, all three major seats are held by Democrats- this includes the Governorship & the two Senate seats held by Elizabeth Warren & Ed Markey, who are both in their 13th year in their respective seats. Moving down the ballot, the remaining congressional breakdown is 9-0 in Democrats’ favor, with 8 of the 9 incumbents running for re-election. The primary elections are set for September 9th, followed by the general election on November 3.
Massachusetts remains one of the most reliably Democratic states in the country, both in federal elections and across much of its political infrastructure. Rooted in a long tradition of liberal governance, strong public institutions, and highly engaged voters, the state has consistently favored Democratic candidates at the national level for decades.
At the federal level, Massachusetts has not supported a Republican presidential candidate since Ronald Reagan. The state’s electorate is heavily concentrated in urban and suburban regions such as Boston, Cambridge, and Worcester, where Democratic support is both deep and reliable. Several structural factors reinforce this advantage. Massachusetts has one of the highest levels of educational attainment in the country, a strong union presence in key sectors, and an economy anchored by healthcare, education, and technology; all of which tend to correlate with Democratic voting patterns. In addition, the state’s political culture places a premium on government competence, public investment, and social services, aligning closely with mainstream Democratic policy priorities.
That said, Massachusetts politics are not without internal competition. While Republicans are largely noncompetitive at the federal level, the Democratic Party itself encompasses a wide ideological range; from establishment incumbents to progressive challengers, as reflected in the state’s Senate race. As a result, the most meaningful electoral contests in Massachusetts often occur in Democratic primaries rather than general elections.
In short, Massachusetts is not a battleground state; it is a Democratic stronghold. The question in 2026 is not whether Democrats will win, but which Democrats will.
Senate
Ed Markey is up for re-election but is facing a challenge from Seth Moulton, the lone House incumbent not running for re-election. Markey, who is 80, has faced calls to retire & turn over the reins to a young upstart, Moulton, 47. Aside from age, Markey has done little to upset voters in the Bay State. The anxieties from prominent liberal figures staying in office for too long, including Biden & Justice Ruth Bader Ginsburg, resonate with democratic voters broadly, yet the polling shows Markey with a solid lead over Moulton.
While elder moments could lead voters to question Markey’s ability before September, the incumbent Senator has a firm grip on his seat heading into 2026. Senator Ed Markey has built a decades-long career rooted in progressive policy, consumer protection, and technological innovation. After serving 37 years in the U.S. House before his election to the Senate in 2013, Markey has established himself as a leading voice on climate change, clean energy, and telecommunications policy. He has authored or co-authored major legislation on fuel efficiency standards, net neutrality, and online privacy protections, while also playing a key role in landmark efforts such as the Waxman-Markey climate bill. His work consistently emphasizes both economic growth and consumer safeguards, particularly in emerging industries and energy markets.
Markey’s longevity in Massachusetts politics stems from his ability to align with the state’s priorities: strong environmental protections, investment in innovation, and a commitment to government oversight in the public interest. His reputation as a policy-driven legislator, combined with a deep connection to Massachusetts’ political identity, has made him a durable and trusted figure among voters. In a state that values both progressive leadership and institutional experience, Markey continues to represent a blend of forward-looking policy and established credibility that resonates with the electorate.
Representative Seth Moulton could emerge as a viable alternative if concerns about Senator Markey’s longevity begin to surface before the primary. A Marine Corps veteran and established member of Congress, Moulton brings a younger profile and a record that blends national security credentials with pragmatic Democratic policy positions. While Markey remains firmly ahead in polling and retains strong support across the state, Moulton’s appeal would likely rest on generational contrast and his ability to position himself as a next-generation leader for Massachusetts Democrats. That said, absent a significant shift in the race, his path remains narrow given Markey’s entrenched advantages.
House
Turning to the House, none of Massachusetts’ nine districts are expected to be competitive in the general election. However, the 6th Congressional District stands out as an open-seat contest, with Representative Seth Moulton pursuing a Senate bid.
In a crowded Democratic primary field, Dan Koh (41) has emerged as the early frontrunner, followed by John Beccia. With limited polling available, fundraising serves as one of the few measurable indicators of candidate strength. Koh and Beccia are the only candidates to surpass the seven-figure mark, giving them a clear advantage in terms of campaign infrastructure and visibility.
Koh’s profile is built on a combination of federal, local, and private-sector experience. During the Biden administration, he served in senior roles at the White House and as Chief of Staff at the Department of Labor, where he helped implement major initiatives related to infrastructure, clean energy, and worker protections. Earlier, as Chief of Staff to former Boston Mayor Marty Walsh, Koh was part of a period marked by economic growth, expanded housing access, and improved educational outcomes.
That breadth of experience, spanning Washington, Boston, and the private sector, gives Koh a well-rounded résumé that appeals to both establishment Democrats and voters focused on governance and delivery. Combined with strong fundraising networks and institutional backing, he enters the race with clear structural advantages. In a district where Democratic voters tend to prioritize competence, policy experience, and coalition-building, Koh is well positioned to consolidate support and secure the nomination.
His main primary opponent, Beccia, presents a contrasting profile centered on private-sector experience and a reform-oriented message. With a background in finance and entrepreneurship, Beccia has emphasized issues such as housing affordability, economic inequality, and government accountability. While that outsider framing may resonate with voters seeking a different approach, Massachusetts Democratic primaries have historically favored candidates with established public-sector experience and institutional ties. In that context, Beccia’s candidacy highlights a clear ideological and experiential contrast, but one that may ultimately reinforce Koh’s advantage as the more traditionally positioned contender.
While Koh is the early favorite, there remains significant time before the primary. Given the field’s size, the race could become more competitive as candidates consolidate support, making it a contest worth watching as it develops.
The remaining districts are held by incumbents who are expected to secure reelection barring any major political shift:
- District 1: Richard Neal
- District 2: Jim McGovern
- District 3: Lori Trahan
- District 4: Jake Auchincloss
- District 5: Katherine Clark
- District 7: Ayanna Pressley
- District 8: Stephen Lynch
- District 9: Bill Keating
Taken together, Massachusetts is unlikely to see any meaningful partisan competition in 2026, with Democrats positioned to retain full control of both the Senate and the House. National political conditions may further reinforce that advantage. Recent polling shows Donald Trump’s approval rating falling into the low 30s amid concerns over the Iran conflict, rising costs linked to tariffs, immigration enforcement controversies, and ongoing backlash surrounding the Epstein files. In a midterm environment where the president’s party often faces electoral headwinds, those dynamics could contribute to a broader Democratic overperformance. In a state as reliably blue as Massachusetts, that would likely translate into not competitive races but comfortable victories for Democratic candidates across the board.
Recent Interviews:
- Ed Markey at a No Kings! Rally- https://www.youtube.com/shorts/k49sITKLruA
- Seth Moulton on the Iran War- https://www.youtube.com/watch?v=o0wCDAcerc0
- Dan Koh announcment video- https://www.facebook.com/danarriggkoh/videos/launching-our-campaign/1505134484025680/
- John Beccia announcement video- https://www.instagram.com/becciaforcongress/reel/DUUYWwVjtCH/?__d=1
Engagement Resources:
- Ballotpedia- serves as an initial go-to for candidates and races at all levels:
- Cook Political Report- CPR evaluates races by competitiveness:
- The CommonWealth Beacon is a nonprofit outlet known for tracking political happenings in the Bay State.
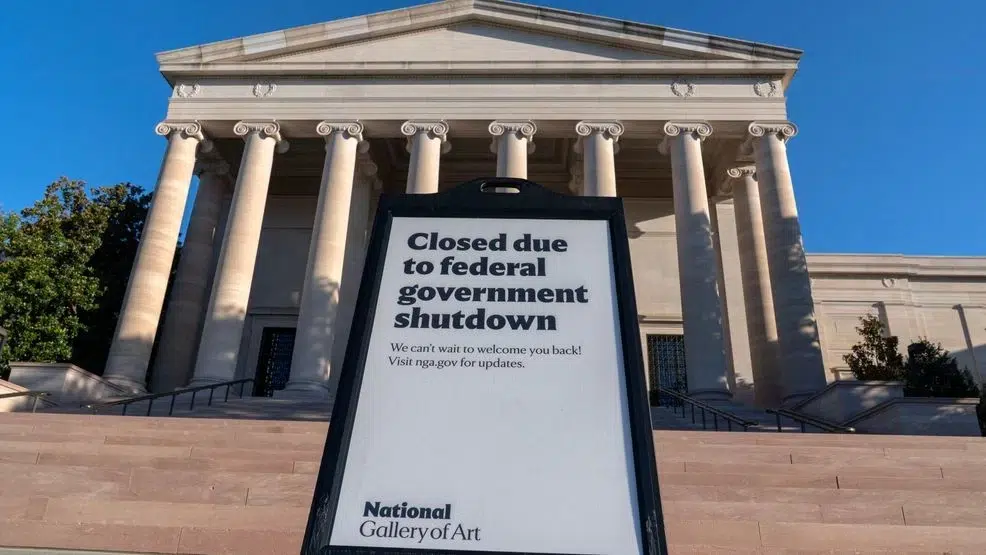
Flying Blind — The Economic Sabotage of the Federal Shutdown (Economic Policy Brief #92)
Economic Policy Brief #92 | Valerie Henderson | April 6, 2026
Summary
While the full federal government reopened in early 2026, the United States remains in a state of economic volatility due to a lingering partial shutdown of the Department of Homeland Security (DHS), now entering its 67th day. The broader 40-day shutdown earlier this year reduced real Gross Domestic Product (GDP) growth by an estimated 1.5 to 2.0 percentage points on an annualized basis, resulting in a permanent loss of activity between $7 billion and $14 billion. Although most agencies have resumed operations, the “data blackout” from late 2025 which included the cancellation of the full October jobs report continues to hamper year-over-year economic forecasting. Today, the crisis has shifted to our borders and airports, where the DHS funding lapse has forced the Transportation Security Administration (TSA) and ICE to operate with severe staffing shortages and delayed pay.
Analysis
The economic damage of these consecutive fiscal crises is compounding. While the Labor Department has resumed most regular reporting, the loss of critical 2025 data sets means that the Federal Reserve and global investors are still working with “incomplete maps.” The Fed’s reliance on data-dependent decision-making is compromised when historical benchmarks from the shutdown period are simply missing or statistically “noisy.”
From a social justice perspective, the current DHS-specific shutdown is particularly localized but intense. While most federal employees received backpay after the general reopening, TSA officers and DHS contractors are currently missing paychecks or receiving them in arrears. At major hubs like George Bush Intercontinental (IAH), wait times peaked at four hours this month as nearly 55% of staff called out due to financial hardship. This forces a reliance on untrained “supplemental” staffing, which advocacy groups argue compromises both worker rights and public safety. Furthermore, the 5.2 million federal contractors impacted by the previous full shutdown remain the “invisible victims,” as they are not legally guaranteed the backpay provided to direct federal hires.
My Opinion
It is ethically unconscionable for the political class to use the stability of the global economy and the livelihoods of civil servants as leverage. The “data blackout” of late 2025 was an act of economic sabotage that we are still paying for today through market uncertainty. Even as the rest of the government functions, leaving the men and women who secure our airports and borders without reliable pay is a failure of leadership.
We are watching a pattern of “economic policing” where the most vulnerable contractors who can’t recover lost wages and frontline officers who can’t pay rent are the ones bearing the cost of partisan ego. We must move toward a system where essential data and essential workers are protected from the theater of budget negotiations. The current strategy of “flying blind” isn’t just a political stalemate; it’s a direct threat to the credibility of U.S. institutions.
Engagement Resources
- Congressional Budget Office (CBO): https://www.cbo.gov/publication/59902
- Center on Budget and Policy Priorities (CBPP): https://www.cbpp.org/research/economy/federal-shutdown-social-impact
- Federal Reserve Board (Data Releases): https://www.federalreserve.gov/monetarypolicy/fomccalendars.htm

Generational Change
Op Ed | Ron Israel | Managing Editor, USRESIST NEWS | April 19, 2026
Look at the evolution of life in America over the last several generations. I did this recently after my daughter came and asked me how she would be able to live well during her later years, when she gets to be as old as I am now. I wanted to be encouraging and optimistic that she would be able to access the same sort of benefits and support as people of my generation; but I wasn’t able to do that.
My generation, those of us born in the period from World War 2 to the mid-sixties, were fortunate enough to live at a time when social security and Medicare benefits were taken for granted, when the cost of housing and health care were reasonable; when companies would offer well financed pension plans, and unions took care of their members after retirement.
Most of us were the sons and daughters of second or third generation immigrants, whose grandparents had come to America from other countries. They started with little in their pockets, then scrimped and saved enough money to perhaps buy a home, or live a reasonably lengthy and well supported life. Their children often became the first in their family’s lineage to go to college, get a good education and a reasonably well paying job.
Our generation also lived at a time of cultural optimism and looking forward. The country had survived World War II and was among the victorious nations. The American dream (of having enough money to own a home and raise a family )was still very possible. The ideal of a democratic society, where all men would be treated equally and achieve “life, liberty and the pursuit of happiness,” was still very much alive, supported by the writings and actions of our political and spiritual leaders. The civil rights movement, the women’s movement, and the movement to end poverty and create a great society were part of the culture in which we grew up. We had a sense that we were part of a society that was building something great; that our individual lives were tied up with the lives of our countrymen and women. We had a sense of a world to which we were all connected; that our well-being was tied to the well-being of other countries and the whole planet.
That culture, dream, sense of social purpose and belonging have pretty much ended. We now look more inward and focus on our own Individual development. The ideal of democracy, while still talked about by some, is not fully understood or grasped by many people. Political leaders seem more interested in clinging to their own power than building a great society. We have become fixated on technology and the so-called benefits it can bring us; engaged on social media with people we don’t interact with in real time
Companies and unions with pension plans are rare. People openly challenge the value and cost of social security and health care for all. Machines are taking away jobs. The cost of housing continues to skyrocket. We no longer are on a common journey but seem to be divided between those in so-called red and blue states. Other countries are now looked upon as competitors or even enemies rather than allies.
So how did we get here? What went wrong? In part we have ourselves to blame. Our generation supported civil rights and the building of a great society. However we also were focused on building the value of our own nest egg to the detriment of caring for the well-being of those in different parts of the country.
All of us were caught up in the seemingly eternal cycle of generational change, when it becomes difficult to sustain the culture, economy, and lifestyle of one generation. My generation barely knew the generation of my grandparents. We inherited their names and vestiges of how they saw life but not their experience. We heard the stories of their coming to America and building a life from scratch. But we never experienced that kind of life; and my grandchildren have little idea of their parents’ parents and even less of who their parents grandparents were; no idea of what life was like before social media, computers, and TV.
We are living in a political era dominated by President Trump and the MAGA Republicans. This era has been made possible by the inability of previous generations to continue their ways of life. If you look back at the history of our country you will see the social, cultural and economic changes that have challenged each new generation to sustain its identity. Perhaps, as Hegel might argue, as our identities continue to evolve, there is some greater good involved in this process of generational change. But I don’t know.
And I don’t know exactly what to tell my daughter when she asks about the future. She won’t have the same old-age support environment as I have had; and certainly not the same as my parents and their parents before them. She will be part of her own generation’s change and response to the world they have been given.
One thing I can say is that it is important for her and her friends to not just think about themselves, but engage with the life challenges and times in which they live; to find social and political ideals like (but not necessarily) democracy that they can get excited about; and actions they can take to make their own lives more meaningful and their country and the world a better place.

Grindr Hosts Networking Event Ahead of WH Correspondents’ Dinner to Advocate for LGBT Policy Change (Social Justice Policy Brief #190)
Social Justice Policy Brief #190 | By Katie Lever | April 21, 2026
LGBT hookup app, Grindr, will host its inaugural White House Correspondents’ Dinner Weekend Party on April 24, one day before the White House Correspondents’ Dinner. The dinner party is set to be a networking event that will bring journalists, policymakers, and members of the LGBT community together at a critical time in LGBT policymaking. It’s a move that many are questioning, given the Trump administration’s hostility toward LGBT populations (even though Grindr regularly sees spikes in usage and even crashes from overuse surrounding republican-centric events). However, given today’s political climate, Grindr’s presence in Washington makes sense.
“Grindr represents a global community with real stakes in Washington,” said Joe Hack, Grindr’s head of global government affairs. “The issues being debated here—HIV funding, privacy and online safety, LGBTQ+ family rights—are daily life for our community.”
They are also policy issues that the Trump administration has sought to defund or slow research for. Since January 2025, LGBT-centric policies from DEI initiatives to LGBT healthcare have been under fierce scrutiny by the Trump administration. Executive orders and presidential memos have been effective in targeting policies that impact access to gender-affirming healthcare, define sex as binary, and negatively impact HIV service delivery to LGBT communities. Trump’s targeting of NGOs has also impacted funding and research for LGBT health issues, which negatively impacts the community.
Policy doesn’t exist in a vacuum, either, and impacts other policymaking agencies. For instance, although the International Olympic Committee’s new sex testing policy, which requires all female athletes to undergo sex testing via gene screening prior to competing, didn’t go through Washington, it was undeniably affected by anti-trans policy that republicans at the state and federal level have been pushing for years. The normalization of LGBT discrimination in policy can be traced back to policies proposed decades ago, and in 2026 alone, there are 669 active anti-trans bills, with 30 state-level anti-trans laws being passed so far this year.
So, while Grindr’s presence in Washington this week might look puzzling on the outside, it makes sense from a policy perspective–and that is the angle Grindr is going for.
“Nobody does connections like Grindr, and WHCD weekend is the most iconic place in the country to make them,” Hack said of Grindr’s presence in Washington next week. “We figured it was time to host.”

The Week That Was: Global News in Review (Foreign Policy Brief #232)
Foreign Policy Brief #232 | By Abran C.

The Iranian-flagged cargo ship Touska is seen as USS Spruance conducts its interception in the north Arabian Sea on April 19, 2026. © Centcom, via Reuters
US & Israel – Iran War Updates
Iran has vowed retaliation after a US destroyer fired on an Iranian-flagged cargo ship in the Gulf of Oman late last week. The cargo ship was attempting to evade a US naval blockade. Tehran condemned the incident as “armed piracy” and warned its forces would respond soon. Oil prices rose and stock futures fell as the markets received conflicting messages about the Iran war and news that the Strait of Hormuz was closed again. As deliberations on ending the war are underway in Islamabad Pakistan, Iran has stated it is not planning to participate in new peace talks with the United States. US President Donald Trump has said the US was sending envoys to Pakistan for talks and would strike Iran unless it unconditionally accepted his terms. The setback in diplomatic talks and increased threats will prolong the war now in its eighth week, which has resulted in thousands of lost lives and created one of the most severe shocks to global energy supplies in history.

A screengrab of a video posted by US Secretary of Defense Pete Hegseth on October 29, 2025, shows the aftermath of a strike on a vessel in the eastern Pacific Ocean [Screengrab/US Defense Department] Al Jazeera
US Strikes in the Pacific
Last week four more people were killed in a US airstrike in the Eastern Pacific, in growing attacks on vessels over the past few months. SOUTHCOM, which is responsible for US military operations in Latin America and the Caribbean, claimed that the four people killed were “narco-terrorists”, but provided no evidence to support the claims. The latest killing of people on board vessels in international waters in the eastern Pacific Ocean and Caribbean brings the overall death toll to at least 175. The attacks began in early September 2025, when US President Donald Trump ordered attacks to stop what was claimed to be Latin American drugboats transporting drugs to the US. International law experts, human rights groups and regional governments have accused the US administration of carrying out extrajudicial killings in international waters, which have likely targeted civilians, often fishing crews, who do not pose an immediate threat to the US.

Displaced people have been crossing into Burundi at the Kavimvira border to escape the M23 advance Image: Jospin Mwisha/AFP/Getty Images
DRC – M23 rebels humanitarian truce
The government of the Democratic Republic of the Congo (DRC) and M23 rebels have agreed to ease aid deliveries and release prisoners, as a push to resolve the years-long conflict that has persisted despite multiple peace deals continues in Switzerland. While the two sides signed a United States-brokered peace agreement in December 2025, fighting has continued. Both sides pledged not to target civilians and to facilitate medical care for the wounded and sick as they noted progress on a protocol for humanitarian access and judicial protections.
The agreement establishes a body to track humanitarian and security developments and monitor potential ceasefire violations. It will include representatives from both the DRC government and the armed group, with support from the United Nations Organization Stabilization Mission in the Democratic Republic of the Congo (MONUSCO). The conflict has seen thousands killed, over a million people seeking refuge abroad and twenty-one million people with-in the country in need of urgent medical, food, and other aid, representing one of the worst humanitarian crises in the world.

Commuters walk on a platform after disembarking from a suburban train at a railway station in Mumbai, India [File: Niharika Kulkarni/Reuters]
India begins world’s largest census
With an estimated population of 1.4 billion, India, now the world’s most populous nation, is launching what is set to be the largest census ever conducted. More than three million officials will be involved in documenting the country’s huge and still growing population. The exercise will be conducted across 36 states and federally-administered territories, more than 7,000 sub-districts, over 9,700 towns and nearly 640,000 villages, Enumerators will gather data on amenities such as drinking water, lighting, sanitation, wastewater outlets, bathing and kitchen facilities, and cooking fuel. In addition, details of accessibility to the internet, television, mobile phones, vehicles and computers will be recorded. The last census in India was held 15 years ago in 2011 since the 2021 Census was delayed because of the outbreak of Covid-19. The process this time around will also include caste enumeration, allowing the counting and categorizing individuals based on their caste affiliation, a politically sensitive issue that has long been debated and absent from census taking since 1931.

Professional Exclusion and the Texas Workforce Crisis
Social Justice Policy Brief #190 | Valerie Henderson | April 6, 2026
Summary
Between March 29 and April 6, 2026, a major workforce crisis intensified across Texas as state regulatory bodies began a coordinated effort to revoke or deny occupational licenses for non-citizens and DACA (Deferred Action for Childhood Arrivals) recipients. Reports indicate that over 6,400 individuals including refugees, healthcare workers, and commercial drivers have already seen their professional credentials invalidated or blocked due to new state mandates aimed at restricting the economic participation of non-citizens. This shift represents a dramatic reversal of long-standing Texas policies that previously sought to integrate these skilled workers into the state’s booming economy to fill critical labor gaps.
Analysis
The social justice implications of this crackdown are staggering, as it creates a “pipeline of exclusion” that targets the economic mobility of minority and immigrant populations. By revoking licenses in essential fields like nursing, construction, and transportation, the state is effectively forcing legally present residents out of their careers and into financial instability. This policy ignores the fact that these individuals have already met the state’s rigorous training and testing requirements; their professional competency is not in question, yet their right to earn a living has been stripped away for political reasons.
This movement has created a ripple effect through the Texas economy. As thousands of commercial driver’s licenses (CDLs) are revoked, the state’s supply chain and logistics infrastructure face new, unnecessary pressures. In the healthcare sector, the loss of qualified nursing staff during a period of already high demand threatens the quality of care in underserved communities. Advocacy groups argue that this initiative is not about public safety or professional standards, but rather about the systematic marginalization of a demographic that has historically been vital to the state’s growth.
My Opinion
It is incredibly frustrating to watch the government go out of its way to stop people from working and contributing to their communities. If someone has put in the work to go to school, pass their professional exams, and earn a license, they should have the right to use those skills to provide for their family. Taking that away is a direct hit on the “American Dream” that we claim to support. This isn’t just about a job; it’s about a person’s identity and their ability to build a stable life for themselves and their children.
Everyone deserves the right to a livelihood. When the state steps in to block that path, it doesn’t just hurt the worker. It hurts the patients who need nurses, the businesses that need drivers, and the neighborhoods that rely on these professionals. It is a backwards policy that chooses exclusion over progress. We should be finding ways to make it easier for hardworking people to enter the workforce and succeed, not creating new bureaucratic traps to shut them out. This kind of “economic policing” is a major step in the wrong direction for Texas and is a clear violation of the social justice principle that everyone should have a fair shot at success based on their skills and effort.
Engagement Resources
- The Texas Tribune: https://www.texastribune.org/2026/04/02/texas-occupational-licensing-non-citizens/
- National Immigration Law Center (NILC): https://www.nilc.org/issues/workers-rights/occupational-licensing-barriers-2026/
- American Civil Liberties Union (ACLU) of Texas: https://www.aclutx.org/en/news/defending-right-work-texas-licensing-crisis
Issues Affecting Democrat Messaging in the Upcoming Midterm Elections (Elections and Politics Brief #204)
Elections and Politics Brief #204 | By Haley Gabrielle Lloyd | March 19, 2026
With the 2026 midterm general elections approaching, analytics show Democrats rebuilding national attention. Though it is early, special election results, voter enthusiasm and new candidates suggest what some analysts call a possible Democratic “blue wave.”
Historically, political analysts look to off-cycle elections and voter engagement metrics as early indicators of national political trends. In recent months, Democrats have performed well in several competitive races. Recently, they have been outperforming in districts that traditionally lean Republican. These results cannot determine national outcomes on their own, but they can reveal shifts in voter engagement heading into midterm campaigns.
The levels of enthusiasm appear to be higher among Democratic voters. According to recent national polling analysis reported by The Washington Post, Democratic voters are more motivated to participate in the 2026 midterms than their Republican counterparts. Off-year elections tend to have lower turnout than presidential contests, so the differences in enthusiasm can greatly influence electoral outcomes.
Several policy issues are driving this engagement. The fight for reproductive rights is still a major force, especially after ongoing legal and political battles over abortion access in many states. Concerns about voter suppression, protecting democracy, and climate policy have also energized progressive organizers and younger voters. At the same time, the Democratic Party is having major debates, especially about U.S. foreign policy. One important debate is about the influence of groups like the American Israel Public Affairs Committee (AIPAC) in primary races. These discussions have revealed ideological divisions within the party, which are now shaping Democratic messaging as the 2026 election cycle approaches.
There are big ideological differences about how strongly the party should push for policy changes. Progressive Democrats are going in hard on federal issues like climate change, student debt relief, universal health care, and stronger labor protections. They are also having more critical discussions on U.S. foreign policy. The focus is on human rights and reducing military spending in some areas. On the other hand, moderate or centrist Democrats tend to lean towards gradual reforms, deliberate spending, and messages about economic stability and bipartisan efforts, especially in states where winning over independent or conservative voters is important.
Another topic of debate is the role of campaign funding and the role of outside political organizations in shaping primary outcomes. Some progressive candidates have criticized the influence of large political action committees and high-dollar donors. They believe that grassroots fundraising better reflects the priorities of the party’s base. On the other hand, some within the party argue that support from established advocacy groups and the traditional fundraising methods are essential to stay competitive in expensive state and federal races. These disagreements continue to shape campaign messaging and the overall direction of Democratic strategy heading into the 2026 midterms.
The party is starting to see the rise of a new generation of candidates. Across the country, more young and first-time candidates are launching campaigns in districts traditionally considered difficult for Democrats. In Texas, State Representative James Talarico, who is still in his thirties, is considered a Democratic rising star among progressives after winning one of the closest-watched Democratic Senate primaries. Campaigns such as Talarico’s rely more on grassroots fundraising and digital outreach strategies than previous Democratic campaigns. His campaign was able to raise almost $7 million in its first 3 weeks, and by the primaries, they raised $13 million. It is reported that 98% of donations were $100 or less. The campaign has also stated that they do not take money from corporate PACs.
While all of this looks good for the Democratic Party, early polling and analytics do not guarantee election outcomes. Midterms tend to pose a threat for the party that holds the presidency. There also has to be consideration for economic conditions or major national events that could alter the political landscape between now and November 2026. However, the combination of younger candidates and voters in competitive races suggests Democrats may be entering the midterm cycle with outstanding political strength.
Recent research shows members of Generation Z and younger millennials are playing a larger role in midterm turnout. The issues driving them to the polls are reproductive rights and climate policy. College-educated suburban voters, especially women, remain a key Democratic constituency in competitive districts. At the same time, multiracial urban associations also continue to shape electoral outcomes. Latino and Asian American populations are among the fastest-growing demographics. The growth in major cities has added the influence of younger and more diverse voters on campaign strategy and messaging.
Engagement Resources
The NALEO Educational Fund works to promote civic participation among Latino voters. It does outreach, leadership development, and public education programs. The group also shares research on Latino political engagement, especially in states with major Latino population growth.
RuralOrganizing.org helps grassroots organizing in small towns and rural areas nationwide. It trains local leaders and promotes civic engagement on economic and community issues. The network aims to strengthen voter participation in places that tend to be left out of national organizing.

2026 Democratic Primary Preview Series: New York
2026 Democratic Primary Preview Series | Nate Iglehart | 4/14/2026
New York often sits in the average voter’s mind as a solid blue state, almost as a homogenous Democrat stronghold. With the recent election of Zohran Mamdani as the mayor of NYC, one wouldn’t be faulted for assuming that the rest of the state is skewed towards the left to some degree. Representatives like Alexandria Ocasio-Cortez, House Minority Leader Hakeem Jeffries, and Senate Minority Leader Chuck Schumer lend credence to this impression.
Much of this is also no doubt due to the cultural significance and liberal disposition of New York City, but outside of the Big Apple, the story is a little more complicated. It is true that both senators from the state have been Democrats since 1998 and that the state has voted for a Democrat in the presidential election since 1988. But in the past few election cycles, there have been multiple house seats that have changed hands, and now the house delegation makeup is 19 Democrats and 7 Republicans.
Some of the more interesting races will likely actually be within the Democratic party as opposed to between the two parties. The issues facing the state extend beyond just NYC, and include extremely high rents and housing prices, crime and safety, education and budgetary woes, and general affordability. The solutions to these issues have split democrats regarding how to solve these issues. For example, Democrats are split between its pro-development wing, which wants to build more housing, and wings more focused on tenant-protection. Centrist elements of the party are also calling for more strict immigration and anti-crime initiatives, further splitting the party.
But there are still races that will be important for Democrats to defend from Republicans. Democrats’ biggest challenge isn’t just flipping seats, it is defending multiple very narrow wins from 2024 and handling a few races that face redistricting. At the end of the day, control of the U.S. House of Representatives may come down to one or two seats, and New York has a couple of races that may decide that control. The primaries will take place on June 23, with the general election occurring on November 3rd.
Currently, the two Senators are Democrats Chuck Schumer and Kirsten Gillibrand. Schumer is arguably one of the highest profile Democrats in the nation and he serves as the current Senate Minority Leader and previously the Senate Majority Leader. Gillibrand is slightly less well known, but serves on the Committee on Appropriations and the Committee on Armed Services. Neither of these two senators are up for election this cycle, and both remain relatively popular.
In the House, there are 19 Democrats and 7 Republicans. In ascending district order, the representatives are as follows: Republican Nicholas J. LaLota (NY-01), Republican Andrew Garbarino (NY-02), Democrat Tom Suozzi (NY-03), Democrat Laura Gillen (NY-04), Democrat Gregory Meeks (NY-05), Democrat Grace Meng (NY-06), Democrat Nydia Velazquez (NY-07), Democrat Hakeem Jeffries (NY-08), Democrat Yvette Clarke (NY-09), Democrat Daniel Goldman (NY-10), Republican Nicole Malliotakis (NY-11), Democrat Jerry Nadler (NY-12), Democrat Adriano Espaillat (NY-13), Democrat Alexandria Ocasio-Cortez (NY-14), Democrat Ritchie Torres (NY-15), Democrat George Latimer (NY-16), Republican Michael Lawler (NY-17), Democrat Pat Ryan, (NY-18), Democrat Josh Riley (NY-19), Democrat Paul Tonko (NY-20), Republican Elise Stefanik (NY-21), Democrat John Mannion (NY-22), Republican Nick Langworthy (NY-23), Republican Claudia Tenney (NY-24), Democrat Joseph Morelle (NY-25), and Democrat Timothy Kennedy (NY-26).
However, there are two incumbent Democrats who are not running for reelection this cycle in Velázquez in the 7th district and Nadler in the 12th. This means that Democrats will have to work a little harder in these races to counter the established Republican candidates who will see this as a rare opportunity. Republican Elise Stefanik in the 21st is also not running for reelection. Out of the 26 races, these are the Democratic names to keep an eye out for:
- District 1: Chris Gallant
- District 2: Patrick Halpin
- District 3: Tom Suozzi
- District 4: Laura Gillen
- District 5: Gregory Meeks
- District 6: Grace Meng
- District 7: Antonio Reynoso and Claire Valdez
- District 8: Hakeem Jeffries
- District 9: Yvette Clarke
- District 10: Dan Goldman and Brad Lander
- District 11:Troy McGhie
- District 12: Alex Bores, Jack Schlossberg, and Micah Lasher
- District 13: Adriano Espaillat
- District 14: Alexandria Ocasio-Cortez
- District 15: Ritchie Torres
- District 16: George Latimer
- District 17: Cait Conley and Beth Davidson
- District 18: Pat Ryan
- District 19: Josh Riley
- District 20: Paul Tonko
- District 21: Blake Gendebien and Dylan Hewitt
- District 22: John Mannion
- District 23: Aaron Gies
- District 24: Alissa Ellman
- District 25: Joseph Morelle
- District 26: Tim Kennedy
Most Competitive Districts for Democrats
There are roughly seven races that will be competitive for Democrats. The first, and the most competitive, will be in the 17th district located in the Hudson Valley. Incumbent Republican Mike Lawler has raised a massive amount of money so far, sitting on $5,209,722 of donations. But even with this war chest, polls and analysts consider this race a true tossup. The biggest question is who in a crowded field of Democratic primary candidates will come out on top. These candidates’ backgrounds range from nonprofit executives to political reporters and cybersecurity and infrastructure experts. Cait Conley and Beth Davidson so far look like the frontrunners, with both having raised over $1 million and the former racking up endorsements from incumbents. The district has voted for Democrats in practically every statewide and federal election save for the 2022 governor race, and before Mike Lawler it was represented by a Democrat in the house since 1983. One key element in this district’s race will be the significant Jewish population, including conservative Hasidic communities in Rockland County. The war in Iran and Gaza will be potent political talking points and can swing this district slightly more towards the right, given many Democrats’ disillusionment with the U.S.-Israel relationship.
Another competitive race will be the 4th district, located in suburban Long Island. Currently represented by Democrat Laura Gillen, this district is the second wealthiest in New York and one of the wealthiest in the country. Similarly to the 17th district, this one leans slightly blue but by a smaller margin. Democrats only won it by 2.3 points in 2024, and before Gillen, the district was briefly held by a Republican. That candidate has yet to declare his campaign, but this race will still be somewhat tight. This race will be a must-hold for Democrats, but with Gillen’s centrist platform and solid focus on local issues, it is certainly possible.
The next competitive district will be the 19th district, a historically competitive seat that flips back and forth between parties. Incorporating the Catskills, Hudson Valley, and greater Capital District, it is largely a white and rural district represented currently by Democrat Josh Riley. Riley, a mix of progressive and centrist policies, won this district by 2.2 points in 2024, and while he is not wildly popular, he is popular enough and both well-funded and well-connected enough to be a key part of Democratic efforts to win the House. He shouldn’t lose this race with all of these factors, but the fact that Democratic planners are still focusing on this district means that they likely also have a little trepidation given how uncertain polls can be. Republicans will likely be looking to flip this seat back regardless of how the rest of New York’s races shake out.
One of those important targets will certainly be the chaotic 3rd district, representing parts of western Long Island. This is the wealthiest district in New York and the fourth wealthiest nationally, meaning that most progressive policies here will struggle. Nonetheless, the district leans towards Democrats, with Tom Suozzi having taken the seat after George Santos’ infamous tenure here. This mess of a political stint by Santos may have played a part in Democrats taking this seat, but it is far from certainty that this will remain blue. The 3rd district has had a litany of both Republican and Democrat representatives, but has been shifting blue lately. Importantly, in the 2024 election, this district voted for Trump while also electing a Democratic representative, making it one of the thirteen across the country that voted this way. Between its wealth and its hyper-urban nature, Suozzi has had to focus on cultivating an image of him being a common-sense Democrat focused on bipartisan solutions. It also didn’t hurt that he pushed for tax breaks and removing double taxation on homeowners. Thankfully for Democrats, this approach seems to have worked and Suozzi is fairly popular. But given how competitive this district has historically been, don’t be surprised if this one comes down to the wire.
From here, the races get slightly less competitive, but still are the biggest targets for upsets on both sides. In the 11th district, drama regarding the constitutionality of a redistricting effort and lawsuits have made a traditionally red district (currently the only one in metropolitan NYC) more open for a Democrat to win. Nicole Malliotakis, the incumbent Republican representative, is a very popular third-term representative and won the last election 64-36. Before her, however, the Staten Island district was represented by a Democrat, a pair of Republicans before that, and then only Democrats from 2013 all the way back to 1945. The district still leans red in both its registered voter numbers and recent voting results, but a lawsuit alleging voter discrimination against minority groups made its way all the way to the Supreme Court before being halted for this cycle, meaning that next cycle, this map may look vastly different. For now, it is still likely a slightly red seat, but with a blue wave big enough, Republicans may not be able to hold onto this district.
In the 1st district, Republican incumbent Nick LaLota, who was re-elected with 55.5% of the vote in 2024, may be at risk of an upset. On paper, this seat looks safe. Located on the eastern end and North Shore of Long Island, including the Hamptons, this district used to be a swing district in the 1990s before leaning more and more Republican since the 2010s. But a December 2025 poll found that 41% of voters supported LaLota while 38% supported the current leading Democratic candidate Chris Gallant. With 20% undecided, this seems to indicate this could be a closer race than previously anticipated, especially as polling aggregators have continually downgraded this seat over the past year from a solid Republican win to a likely Republican win. That being said, the fight is certainly uphill. LaLota has raised $2,404,492, around eight times as much as Gallant has. LaLota is also a two term representative, and represents a collection of fairly wealthy and middle-class towns that have historically voted red. If the winds continue to blow in Gallant’s direction, this could be an interesting race to watch.
Another potential upset race will be in the 21st district. Similarly to the 1st, this race sees incumbent Republican Elise Stefanik facing a surprisingly strong campaign from Democrat Blake Gendebien. A historically blue district, Stefanik has changed the game since she won this seat in 2015. But she’s set to shift the paradigm once more, now in the other direction. After having nearly been nominated by Trump to be the United States Ambassador to the United Nations in 2024, she decided in December 2025 that she would not run for reelection this cycle, leaving the race more open than expected. Republicans have rallied around businessman Anthony Constantino and he has raised over $5 million in a short time. But Democratic challenger and dairy farmer Blake Gendebien has also managed to raise an enormously surprising $4 million over the same time, making this a last minute addition to the watchlist. Don’t be fooled, the district still leans slightly red, but without an incumbent Republican, Gendebien may just be able to shock observers here.
Finally, there is one race that will not be important in the fight for control of the House, but will be very interesting to watch in order to see where internal Democratic politics is heading. In the 12th district, the district represented Midtown Manhattan and both the Upper East and West Sides. It is the most Democratic district in New York and the 9th most in the country, while also sitting high on the rankings when it comes to average wealth. As a result, the extremely crowded field has a lot of money poured into it, with four candidates raising at least $1 million already. There is a candidate focusing on big-tech regulation paired with progressive social issues, there is an establishment Democrat, there is a younger generation-focused candidate who also happens to be a grandson of John F. Kennedy, and then there is a center-left, anti-Trump coalition candidate. Each has backing and momentum, but seeing as incumbent Jerry Nadler is not running for reelection, this will be an interesting test lab for the near future of Democratic politics in elite, urban districts.
Most Competitive New Jersey Democrats in 2026
Cait Conley: NY-17
Cait Conley, 39, is a former U.S. Army combat veteran and former director of counterterrorism for the National Security Council. A West Point graduate and Hudson Valley native, Conley is leveraging her military and public service career to push into politics. After deployments to Afghanistan and Iraq across her 16-year-long career, she is focusing her campaign on issues such as lowering costs, cleaning up corruption, affordable healthcare, infrastructure, and treating climate change as a national security issue. In a crowded race, Conley has managed to raise the most money and gather the most endorsements out of any remaining candidate. $1,914,138 raised is nothing to scoff at, and when paired with a host of endorsements from current representatives and organizations, Conley has a lot of momentum going forwards. In particular, this district’s large Jewish population may actually play in Conley’s favor, despite this voting bloc often voting for conservatives. Conley’s experience in the Middle East and with counterterrorism may yield her some goodwill here, and in a district that has historically swung blue, she has a good chance of flipping this seat back.
Recent Interviews
Cait Conley on her NY District 17 House Campaign, Trump, Hegseth and the Illegal Iran War
Beth Davidson: NY-17
The other main contender in the 17th district is Beth Davidson, a 52-year-old Rockland County legislator. Davidson has deep roots in the district, having been a staunch activist when it comes to housing advocacy and administrative work. Between her time at the YMCA, her synagogue’s board, and the Environment Committee and Task Force on Water Resources Management, Davidson truly has experience in a lot of different facets of public service. Her platform is mainly focused on housing affordability, the cost of living, infrastructure, and access to things like healthcare and abortion rights. On the campaign front, she is a seasoned politician. She has ran and won multiple local level campaigns, and this time around she has raised an impressive $1,490,848 through the end of 2025. While she has less endorsements, the people of the district may resonate with her long career of local leadership more than Conley’s, and her Jewish background will help pull that conservative Hasidic community towards her campaign. While money still matters a lot in elections, and she is second on this front, local trust often is a great counter. In the end, the real question will be how much voters want their representative to play a part at the national level versus at the local level. And if they lean towards the local level, Davidson will have a lot more support and a better chance at winning the seat.
Recent Interviews:
Rockland County Legislator Beth Davidson on Bid for Congress | PIX on Politics Daily
Laura Gillen: NY-04
Out in a quiet and suburban Long Island district, incumbent Laura Gillen, 56, looks out on an empty field of Republican candidates. And yet, poll aggregators only give this district a slight blue lean. Having won in 2024 by a 2.3 point margin, the former lawyer and law professor has been a staunch centrist. She declined to congratulate Zohran Mamdani’s mayoral win, she broke ranks with Democrats to pass the Laken Riley Act, she voted to censure Democratic congressman Al Green for speaking during Donald Trump’s State of the Union Address, and she recently voted to pass extra funding to ICE. Her platform aims to focus on current Democratic priorities like the cost of living crisis and local investment towards healthcare and infrastructure, while also courting conservatives with more law enforcement-oriented policies and an explicit rejection of the Democratic Party’s left wing. While this might turn off younger voters, it will certainly work in a very wealthy district that swings between parties. Gillen certainly has money of her own; she’s raised $2,858,864 already and has likely not had to spend very much so far. She will certainly win the primary, but if Republicans run Anthony D’Esposito, the previous representative, she will have to work quite hard to hold the seat. Nonetheless, polls suggest she has a slight edge, and depending on whether a blue wave is explicitly anti-ICE or not, she could either ride it to victory or die by it due to her voting record.
Recent Interviews
Rep. Laura Gillen on government shutdown and more | The Point Full Interview 10.5.25
Josh Riley: NY-19
Josh Riley, 45, is the incumbent representative in this historically competitive district. He was able to flip the district with 51.1% of the vote in 2024, and now he is looking to build on this success. Coming from a working-class background in upstate New York, Riley attended Harvard Law School before taking roles in the U.S. Department of Labor, the U.S. Senate Judiciary Committee, and as a counsel to former Senator Al Franken. This is his first time now in office, and he has pushed a slew of policies that straddle the line between progressive economic populism and more moderate social and immigration policies. Riley’s main focus, like many Democrats, has been on the cost of living, campaign finance reform, healthcare, and protecting democracy. With endorsements from many organizations and a whopping $3,129,176 raised through the end of 2025, Riley is in a solid position as the campaign ramps into high gear. But Republicans will try to target this seat, and while the main challenger hasn’t raised a ton of money yet, he is a state senator with endorsements from Trump, Speaker Johnson, and Representative Mike Lawler. This will be a close race based on how previous election cycles have gone, and if Republicans see an opportunity, Riley may need to work hard to fend off his opponent.
Tom Suozzi: NY-03
Tom Suozzi, 63, is a lifelong public servant. A native to this Long Island district, his father was the mayor of Glen Cove, as was Suozzi himself for a time. He was then elected to the House in 2016 and reelected in 2018 and 2020. In 2022, he attempted to run for the Democratic gubernatorial nomination in 2022 but lost to incumbent governor Kathy Hochul. But in 2024, he managed to re-win this district 52-44, flipping this seat back for Democrats. In terms of policy, Suozzi has some commonalities with Riley and Gillen. He is focused primarily on affordability through reducing taxes, he strikes a moderate tone on immigration, he backs police funding and extending ACA tax credits, and bipartisanship and pushing back against the left wing of the party are both core to his political identity. All of this has thus far played well in this wealthy district, and there is no reason to believe that this won’t continue. Suozzi has immaculate name recognition and local connections in this district, he has raised almost 10 times the amount as his main Republican opponent (Suozzi is sitting on $3,246,484 through 2025), and after Santos’ tenure, the sense of stability that Suozzi has brought will likely earn him some goodwill from independent voters. Unless the expected blue wave in November doesn’t materialize, Suozzi should be expected to win this race.
Chris Gallant: NY-01
In contrast to Tom Suozzi’s career, the 36-year-old Chris Gallant has served the public in almost every way besides politics. A former New York Army National Guard who served in the Middle East, a Black Hawk helicopter pilot, a FAA air traffic controller and leader of his union, and a volunteer firefighter, Gallant aims to bring competence and accountability to this race and win a surprise victory against incumbent Republican Nick LaLota. In order to do this, Gallant has adopted a more moderate platform than many other Democrats in a bid to win voters in a district that went Trump’s way by 10 points. He hits the affordability and healthcare points like many other candidates, but he also aims to invest in coastal protection, something important for Long Island, and explicitly is running against what he calls “political infighting” and a lack of results from elites in DC. His efforts have yielded a lot of hope for Democrats, with a recent poll finding that 41% of voters supported LaLota while 38% supported Gallant. This is far closer than anticipated, but it will absolutely still be a tough fight for Gallant. LaLota has an incumbent and fundraising advantage in a red district. Additionally, Gallant’s identity as openly gay may or may not rub more conservative voters the wrong way. If LaLota’s popularity continues to slip, Gallant may just be able to upset him and win the seat, but both polling and betting odds are not particularly in his favor at the moment. Nonetheless, keep an eye on this race as we get closer to November.
Blake Gendebien
Blake Gendebien, 49, has made quite a stir in the race in the 21st district. A dairy farmer and lifelong resident of Lisbon, NY, he has thus far ran a campaign that may just become a model for how Democrats can win rural red districts. Besides being a dairy farmer, he is a school board member, the Vice Chair of a major regional dairy co-op, and founded a pediatric cancer nonprofit. This background of service and working-class upbringing has influenced his policy platform. Gendebien’s priorities are supporting farmers, protecting small businesses, and general rural economic development, but he also wants to push for anti-corruption measures, expanding healthcare access in rural areas, and working across the aisle to get things done without getting too much into the weeds ideologically. While none of this by itself would make much of a stir in one of the reddest NY seats, his massive fundraising efforts have turned heads. His campaign has raised $4,051,856, and is closing in on the $5,005,073 Republican candidate Anthony Constantino has raised. Constantino does not have the incumbent advantage, as the representative here, Elise Stefanik, is stepping down. This race may be Democrats’ best chance at retaking this seat since 2012, when they last controlled it. That being said, Gendebien will have a tough fight on his hands, as Republicans will almost certainly see this seat as a must-win in New York. While polling aggregators have increasingly pushed their predictions closer to a tight race, polls still lean slightly towards Constantino, so keep an eye out for data as the summer comes and goes.
Recent Interviews:
CBS6 speaks with NY-21 candidate Blake Gendebien
Alex Bores: NY-12
The first of three leading Democratic candidates in the Midtown Manhattan district, Alex Bores, 35, is an indicator for a potential future for the Democrats. Bores himself is a fifth-generation New Yorker who was a software engineer at Palantir before working in various fintech startup roles. He also was elected to the New York State Assembly in 2022, where he helped pass the AI regulation legislation (RAISE Act). With a master’s degree in computer science, he is focusing heavily on ai regulation and is best understood as a technocratic progressive. Bores is pushing for strong regulation and safety standards for AI companies, as well as countering deepfakes and job displacement. Outside of AI, Bores wants to make NYC more affordable through expanding the housing supply, he wants to strengthen democratic institutions and (interestingly) limit the influence of wealthy interests, and he strikes a pro-worker tone based on concerns about tech-driven inequality. The reason he is a frontrunner is because he has both racked up endorsements from state and federal legislators and he has raised the most in the race by a wide margin at $2,236,328. In fact, he raised $1,200,000 in the first 24 hours, but the vast majority of it was from outside of the district. With strong fundraising and a local base, Bores seems to be a favorite. But time will tell how his less locally-rooted donor base and his competition will hinder his ascent to the seat. Both of his rivals have strong campaigns, and if he manages to beat them, he could be a preview of what mainstream urban Democratic politics could be.
Recent Interviews:
Why Is The AI Industry Afraid Of Alex Bores? | Lever Time
Jack Schlossberg: NY-12
Next up in this race is Jack Schlossberg, the 33-year-old political commentator and author. The only grandson of President John F. Kennedy, Schlossberg represents the generational change Democrat in this race. He studied at Yale, Harvard Law School, and Harvard Business School before becoming a Vogue political correspondent and author. Without any traditional governing experience, Schlossberg’s campaign is focused on the aforementioned generational change, the cost of living, democracy and anti-corruption, and climate and civic engagement efforts. This platform is one that hinges on a sense of idealism and renewed faith in politics, and Schlossberg has leaned into this by vowing not to take corporate PAC or super PAC money. Despite this, he still has managed to raise $1,117,588 with a lot of grassroots donations. All of this has led to Schlossberg actually leading in the race according to multiple polls. While they all highlight large undecided blocs, the polls show a 7 to 10 point lead for Schlossberg as of February. With massive name recognition and a strong social media presence appealing to local voters, he certainly has the “vibes” part of running a campaign down. What remains to be seen is whether his lack of a detailed policy platform and governing experience irks voters as the primary nears.
Recent Interviews:
Extended interview: Jack Schlossberg
Micah Lasher: NY-12
Micah Lasher, 44, is bringing political experience and establishment support to this race. He is a freshman New York State Assemblymember, but is also a former Director of Policy for Governor Kathy Hochul, Director of State Legislative Affairs for Michael Bloomberg, aide to incumbent Representative Jerrold Nadler, and former chief of staff in the NY Attorney General’s office. Throughout all of these positions, he has focused on housing reform, minimum wage increases, gun control, and abortion protections. All of these, plus additional focuses on the cost of living, abolishing ICE, and fighting Trump-era policies, make up his policy platform. Lasher also enjoys endorsements from many of his previous bosses and has the highest fundraising potential with Michael Bloomberg’s support. He already has the second-most raised at $1,374,760, and with deep governing experience, he will certainly appeal to older voters and more mainline Democrats. But without something to make him stand out besides his experience, this NYC district may just have gotten a taste of Zohran Mamdani’s politics and push for someone more progressive than Lasher. If this happens, Lasher may just end up being the control experiment for onlookers to measure this race by. But if this isn’t the case, Lasher stands in a strong position to win the race if this becomes a financial battle of attrition.
Recent Interviews:
Full interview with U.S. House candidate Micah Lasher | The Point 3.8.26
Engagement Resources:
- Ballotpedia- serves as an initial go-to for candidates and races at all levels:
- Cook Political Report- CPR evaluates races by competitiveness:
- The New York Times and City & State New York are both great local resources for coverage of elections and issues facing New York.

2026 Democratic Primary Preview Series: New Jersey
2026 Democratic Primary Preview Series | Nate Iglehart | 3/29/2026
After the 2024 election there was talk of New Jersey having become a swing state. For the first time since George H.W. Bush, a Republican president, had been within 5 points of taking the state (Trump still lost, however). Before then, almost every presidential election had gone blue by around 14 points. But looking deeper, there are some Republican strongholds within the state that had been, and continue to, gain ground in house and gubernatorial elections. That being said, since 2020 and especially since 2024, New Jersey may start swinging back towards the Democrats. There are a few districts which have recently had both Democratic and Republican representatives, and with a potential blue wave looming, there may be a couple seats that could help swing control of the house. The primary elections will be held June 2, 2026, with the general election taking place on November 3, 2026.
The issues facing New Jersey favor what many Democratic candidates have been focusing on across the country. Primarily, voters are concerned about affordability (in the form of property traces and the cost of living), healthcare, infrastructure, and a large state-level budget deficit. But New Jersey has some of the highest tax burdens, including a high top marginal personal income tax rate of just under 12%, meaning Republicans have the upper hand here. Democrats have controlled both houses of the New Jersey Congress since 2004, meaning the blame can fairly squarely fall on them in the eyes of many voters. A key dynamic will be just how important of an issue this becomes in the light of a host of other more pressing issues, and as other neighboring states like New York have persisted through high income taxes and even slightly raised the top marginal tax rates.
Currently, the two Senators are Democrats Andy Kim and Cory Booker, with only the latter up for election this cycle. Booker, first elected in a 2013 special election and then re-elected in 2014 and 2020, is running third full term in office and is likely to win. He is one of the most notable Democrats of late, having made many media appearances critical of the Trump administration and also still riding some name recognition from his 2020 presidential campaign. Booker currently serves on four committees: the Committee on Agriculture, Nutrition, and Forestry, the Committee on Foreign Relations, the Committee on Small Business and Entrepreneurship, and the Committee on the Judiciary. His platform has always centered on social justice, criminal reform, and healthcare & social policy, but this cycle he is leaning heavily on an economic platform focused on eliminating federal income taxes on the first $75,000 of income for many Americans, expanding tax credits, and raising taxes on the rich. WHen it comes to fundraising, there is no better than Booker. $30,106,071 has been donated to his campaign through the end of 2025, and when combined with his high popularity and his importance, Booker is all but assured to retain his seat.
In the House, there are eight Democrats, three Republicans, and one vacancy in the 11th district. In ascending order, the representatives are Democrat Donald Norcross, Republican Jeff Van Drew, Democrat Herb Conaway, Republican Chris Smith, Democrat Josh Gottheimer, Democrat Frank Pallone, Republican Thomas Kean Jr., Democrat Rob Menendez, Democrat Nellie Pou, Democrat LaMonica McIver, and Democrat Bonnie Watson Coleman. Out of the twelve races, these are the Democratic names to keep an eye out for:
- District 1: Donald Norcross
- District 2: Bayly Winder
- District 3: Herb Conaway
- District 4: John Blake and Rachel Peace
- District 5: Josh Gottheimer
- District 6: Frank Pallone
- District 7: Rebecca Bennett, Tina Shah, Miachel Roth and Brian Varela
- District 8: Rob Menendez
- District 9: Nellie Pou
- District 10: LaMonica McIver
- District 11: Analilia Mejia
- District 12: Brad Cohen and Jay Vanigankar
Most Competitive Districts for Democrats
Most districts are safe in the hands of the incumbent parties largely because of both how the districts are drawn and how popular those incumbents are. However, there are four districts that will likely be “battlegrounds” in 2026.
The first is NJ-02, where Republican Jeff Van Drew is the incumbent. He was first elected as a Democrat in 2018, but announced the following year that he would be switching parties. The district is New Jersey’s largest geographically and encompasses Atlantic City. What makes this district unique is that it has shifted to the right ever since the 90s, and despite going Obama’s way in both elections, has voted for Republican candidates almost every statewide and federal election since. Van Drew, who was re-elected with 58.1% of the vote in 2024, is facing three main Democratic challengers. Additionally, Van Drew’s popularity in some polls has dropped down to 42%, with a plurality indicating that they would be open to a new representative. A candidate who embodies that “new blood” archetype might just be able to reverse the district’s rightward swing.
The next district to keep an eye on his NJ-07. The incumbent is Republican Thomas Kean Jr., who was re-elected with 51.7% of the vote in 2024, but he is facing a swatch of potential Democrat opponents who are well funded. In the Democratic primary are figures such as healthcare executive and former navy aviator Rebecca Bennett, former chief of staff for the Small Business Administration Michael Roth, former senior advisor to the U.S. Surgeon General Tina Shah, and former chair of the New Jersey Forward Party Brian Varela. This district has flip-flopped between Democrats and Republicans over the past several election cycles, and with a plurality of voters disapproving of Kean’s work thus far combined with such a narrow win in 2024, it is likely to flip again. With the northwestern district, which has become more ethnically diverse over time, being one of the most affluent congressional districts in the United States, Democrats may have to tweak their standard messaging to improve their odds here. But Kean has faced a lot of pressure due to his political closeness to Trump as well as a lot of virtual town halls instead of talking to voters in person. This will be the seat Democrats likely focus on the most.
The final district that Democrats will focus on differs from the previous two. NJ-09 will be a defensive battle, with incumbent Democrat Nellie Pou fighting to remain after being elected with only 50.8% of the vote in 2024. The district is entirely urban, stretching from Pompton lakes to northern Newark and the Hudson River-adjacent town of Cliffside Park. In the 2024 election, the district shifted dramatically to the right, voting by 1.1 points for Trump after having previously voted for Biden by 19 points. Pou still managed to win her election, but the winds were clearly shifting. That being said, much of the vote was driven by the district’s large Hispanic population, which truly helped in Trump’s 2024 election. Since then, it is highly likely that Trump has burned through any goodwill he may have had with this constituency due to his immigration policy and failure to address affordability. This seat will no doubt be close as Republican strategists see this as a district they can win back by labeling Pou as out of touch. Time will tell if a blue wave and good donor relations thus far will manage to keep Pou in office.
Most Competitive New Jersey Democrats in 2026
Bayly Winder: NJ-02
Bayly Winder, 33, is a former foreign affairs officer and Biden appointee who has branded himself as a bipartisan and pragmatic candidate. Those two facets are key to his plan for winning a district that leans slightly red. His policy focuses are centered around lowering the cost of living, protecting Medicaid and social services, anti-corruption and government reform, and a foreign policy that is in favor of foreign aid and free trade. His campaign has tried to be an antithesis to Van Drew’s by promising in-person town halls and more direct constituent engagement. Winder has also tried to pursue that “outsider” stance by criticizing both parties’ failures to address issues and corruption on both sides. He doesn’t quite have the laundry list of endorsements other candidates might, but in this race he has the most money, having raised $451,845 through 2025. On paper, this campaign seems pretty solid, but his connections to Biden’s administration will likely hurt him more than it will help him. His credentials and his bipartisan focus will definitely gain him ground, and he likely will win the primary, but in a general election Winder will have to work hard to earn the trust of the constituency.
Michael Roth: NJ-07
The first of a few candidates covered in this brief that will be running in this district, Michael Roth is a strong contender. Roth, who is in his mid-thirties, is a community investment expert who served briefly atop the U.S. Small Business Administration (SBA) under Joe Biden. His campaign is also focused on pragmatic center-left policies. Issues like making NJ more affordable, cutting middle-class taxes and increasing corporation taxes, increasing the housing supply and reforming zoning, and lowering energy costs through modernization all feature prominently in his platform. What makes Roth stand out is his experience at high levels of both the public and private world. It also doesn’t hurt that he has raised a respectable $610,278 so far and is a New Jersey native. But neither of those facts alone will win him the crowded primary, which is the main hurdle. It is important to note that in early March, members of the Summit Democratic municipal committee held a straw poll in the race in which Roth emerged as the winner. Yet it is early in the race, and there is still plenty of time for Roth to gain daylight between himself and the rest of the candidate pool or to flame out and be buried under the weight of many competing personalities.
Recent Interviews:
Brian Varela: NJ-07
Brian Varela, 36, is seeking to pull on the heartstrings of voters in this district. A first-generation American, Varela grew up in the working class and he emphasizes this “lived experience” narrative. After graduating from Kean University and UNC, he built a successful marketing company and later expanded into early education businesses. Varela has long been a Democratic organizer and tried to win the 2022 congressional primary here as a third-party candidate but now he is firmly a democrat. His policy focuses are on the cost of living, universal healthcare, childcare and family policies, pushing back against ICE, and acting as an outsider against political elites. Between his compelling personal narrative, business success, and outsider positioning combined with some increasingly popular progressive policies, Varela is looking to take advantage of Kean’s weaknesses and flip this seat. But without elected office experience and in a crowded field with candidates with similar positions, his personal narrative will have to do a lot of heavy lifting. So far, he has racked up endorsements from everyone including county Democratic chairs to organizations like Peace Action and the mayors of Sparta and Newark. He also has raised the second most by a Democrat in the race, riding high on $1,759,731. While he may not be the favorite yet, his story and background pair well with his policies and the issues facing New Jersey today. As we approach the primary election, keep an eye out for Varela to make a challenge to the more establishment Democrats in this race.
Recent Interviews:
Brian Varela OneNJ7 Meeting July 2025
Rebecca Bennett: NJ-07
The favorite at the moment is probably Rebecca Bennett. Bennett, a Navy helicopter pilot and aircraft commander who served for over 15 years, is running a tight campaign that has raised an inordinate amount of money. Her $1,943,974 is the most in this race, and is surprising given her lack of government or political experience. Bennett also worked in healthcare startups and larger healthcare companies, and this is a major policy area of hers. She wants to expand access to care, lower costs, and improve patient outcomes, but the rest of her platform is more generic. She values national security, and wants to combat the rising cost of living, but her website is more vague about exactly how she wants to accomplish these. While this gives Bennett more flexibility down the line, she will need to eventually sort out these questions. She does have some policies regarding environmental protections and resilient infrastructure, as well as combating the influence of special interests, but her campaign is more profile than policy-based. What makes her the favorite is her ability to fundraise without connections and run as a pragmatic, electability-focused Democrat with military precision and a healthcare worker’s focus on outcomes. With Roth and Varela breathing down her neck, she is still a long way from being a shoe-in, but if she gains momentum she may be hard to stop from winning the primary.
Recent Interviews
Nellie Pou: NJ-09
Nellie Pou, 69, is a well-known and long-serving New Jersey Democrat. Pou has one of the longest political resumes in NJ, starting as the Deputy Speaker of the NJ Assembly in 1997 before serving in the State Senate after 2012 and now in the U.S. House. Before those elections, she worked in the Paterson city government as a business administrator, youth program coordinator, and human services director. She was also the first Latina from New Jersey elected to Congress, a title that has and will win her some goodwill in her district. Pou has also positioned herself as a broad coalition-builder with appeal amongst moderates, something that can only help her in tight races like this. Her policies are grounded, focusing on healthcare and social services, expanding access to education and workforce development, social justice and immigrant protections, government funding for local programs, and infrastructure. That last area is important to Pou, as she serves on the Transportation & Infrastructure Committee, as well as the Homeland Security Committee. By running a low-drama campaign, she forces voters to look at her resume and political success thus far, which is a solid move. She also has vast local fundraising networks and has raised $1,773,275, dwarfing her Republican counterparts. But with her slight win in 2024, this seat is still not safe. The district is trending more competitive, and her establishment stances don’t win her support amongst both Republicans and progressives. If Pou wants to hang on to her seat, she will need to make sure that her constituents are able to trust her to continue representing them well and by ensuring that her Republican counterparts are not just extensions of Trump but their own people. Unlike other districts, connections to Trump may not be as big of a hindrance for Republicans given voters here liked Trump. But regardless, a blue wave may just give Pou the space to breathe she needs to retain her seat.
Engagement Resources:
- Ballotpedia- serves as an initial go-to for candidates and races at all levels:
- Cook Political Report- CPR evaluates races by competitiveness:
- The New Jersey Globe and the New Jersey Monitor are both great local resources for coverage of elections and issues facing New Jersey.

Space Junk and Corporate Accountability in Orbit (Foreign Policy Brief # 231)
Foreign Policy Brief #231 | By Inijah Quadri | April 13, 2026
Policy Issue Summary
Space exploration has transitioned from a public endeavor driven by international cooperation to a heavily privatized industry dominated by billionaire-backed mega-corporations. At the center of this shift is Low Earth Orbit (LEO), defined by the Inter-Agency Space Debris Coordination Committee (IADC) and NASA as the region of space at an altitude of 2,000 kilometers (1,240 miles) or less. Low Earth Orbit, once viewed as a pristine global commons, is rapidly becoming a celestial dumping ground. The exponential deployment of satellite megaconstellations by private tech monopolies has drastically accelerated the accumulation of space junk, raising profound environmental and safety concerns. While these networks boast of bridging global connectivity gaps, their unchecked proliferation commodifies the orbital environment, prioritizing corporate dominance over the long-term sustainability of the cosmos.
Space junk—comprising defunct satellites, spent rocket stages, and millions of fragmentation debris pieces—poses an existential threat to future space operations. The European Space Agency (ESA) maintains a comprehensive, real-time “map” and census of this congestion, illustrating a dense shroud of objects that grow more crowded by the hour. Operating at orbital velocities, even centimeter-sized fragments carry the kinetic energy of an anvil dropped from a skyscraper. The European Space Agency’s 2025 Space Environment Report indicates that there are over one million debris objects larger than a centimeter currently orbiting Earth. This congestion risks triggering the Kessler Syndrome, a theoretical cascade of self-sustaining collisions that could render specific orbital bands completely unusable for generations, cutting humanity off from vital space-based public services like climate monitoring and global navigation.
Recent deregulatory trends have only exacerbated the crisis. In early 2026, the Federal Aviation Administration abandoned proposed rules that would have strictly mandated the safe removal of commercial rocket bodies within a set timeframe. Justified under the guise of maintaining American dominance in space, the withdrawal of these regulations exemplifies a glaring failure to hold private capital accountable. By allowing private entities to externalize the environmental costs of their operations, the current policy landscape fundamentally gambles with public safety and the equitable use of outer space.
Analysis
The privatization of Low Earth Orbit represents an aggressive enclosure of the commons, where profit-driven entities are permitted to pollute a shared human resource with minimal oversight. Despite the gravity of the situation, there is currently no singular global “orbital police” force with the power to issue binding mandates. The closest technical authority is the IADC (Inter-Agency Space Debris Coordination Committee), which currently consists of 13 member agencies, including NASA (USA), ESA (Europe), JAXA (Japan), CNSA (China), and ISRO (India). While the IADC is the global authority on how to mitigate debris, it functions as a technical body rather than a regulatory one. It works through a Steering Group and four specialized Working Groups—Measurements, Environment, Protection, and Mitigation—to reach a scientific consensus on “best practices.” However, these consensus-based guidelines only carry weight if individual nations choose to codify them into their own domestic laws.
The structural incentives of late-stage capitalism drive companies to launch as many satellites as quickly as possible to secure market share, creating an orbital house of cards. SpaceX’s Starlink alone accounts for thousands of active satellites, and recent data highlights that their network was forced to execute over a hundred thousand collision-avoidance maneuvers in just a six-month window. This staggering figure illustrates an unsustainable operational tempo, placing the burden of collision management entirely on reactive measures rather than proactive, structural regulation.
Regulatory frameworks have failed to keep pace with the hyper-commercialization of space. Current enforcement mechanisms remain dangerously weak, essentially functioning as mere slaps on the wrist that corporations can easily absorb as the cost of doing business. For instance, the Federal Communications Commission issued its first-ever space debris fine to Dish Network for failing to properly deorbit a satellite, but the penalty was a meager financial sum that completely fails to deter multibillion-dollar enterprises from future negligence. To bridge this gap, policy experts have proposed the creation of an International Space Traffic Management (STM) organization—a centralized body that would treat orbital paths as finite natural resources, similar to how maritime or air traffic is managed globally.
To prevent the Kessler Syndrome from becoming an imminent reality, policymakers and international bodies must urgently pivot from corporate appeasement to stringent, enforceable governance. Treating Low Earth Orbit as an environmental zone requiring rigorous ecological protection is paramount. This necessitates the implementation of punitive taxes on debris generation, the mandated integration of zero-debris technologies, and strict international caps on the number of satellites a single entity can operate. The European Space Agency recently adopted a Zero Debris approach, which mandates aggressive collision avoidance and strict post-mission disposal within five years, and serves as a foundational blueprint.
However, technological fixes alone cannot resolve what is fundamentally an issue of unchecked power and inequitable resource distribution. True orbital sustainability requires democratizing space governance, ensuring that the interests of marginalized communities, independent researchers, and future generations outweigh the imperialistic ambitions of a few dominant spacefaring corporations. Stakeholders must organize globally to establish binding treaties that outlaw the monopolization of orbits and enforce massive financial penalties on polluters, ensuring the space frontier remains a shared realm for the benefit of all humanity rather than an exploited playground for private capital.
Engagement Resources
European Space Agency Space Debris Office (https://www.esa.int/Space_Safety/Space_Debris): Leading international research on space environmentalism, collision avoidance strategies, and the Zero Debris initiative aimed at mitigating orbital pollution.
Union of Concerned Scientists (https://www.ucsusa.org/resources/satellite-database): An advocacy and research organization maintaining a comprehensive database of active satellites, analyzing the impacts of commercial congestion and the corporatization of space.
Outer Space Institute (https://outerspaceinstitute.ca/): A network of transdisciplinary space experts focused on identifying and addressing challenges related to space governance, debris mitigation, and the equitable use of orbital resources.
Secure World Foundation (https://swfound.org/): An organization promoting cooperative solutions for space sustainability, focusing on international policy frameworks to address orbital debris and challenge unilateral space traffic management.
Space Court Foundation (https://www.spacecourtfoundation.org/): An educational nonprofit advocating for the development of space law and policy, focusing on holding private entities accountable for their activities in outer space.
