The mid-term 2026 elections provide an opportunity for the Democrats to become the majority party in the House of Representatives and possibly the Senate. Polls suggest that President Trump’s popularity is declining and that the Dems have an opportunity in the mid-terms.
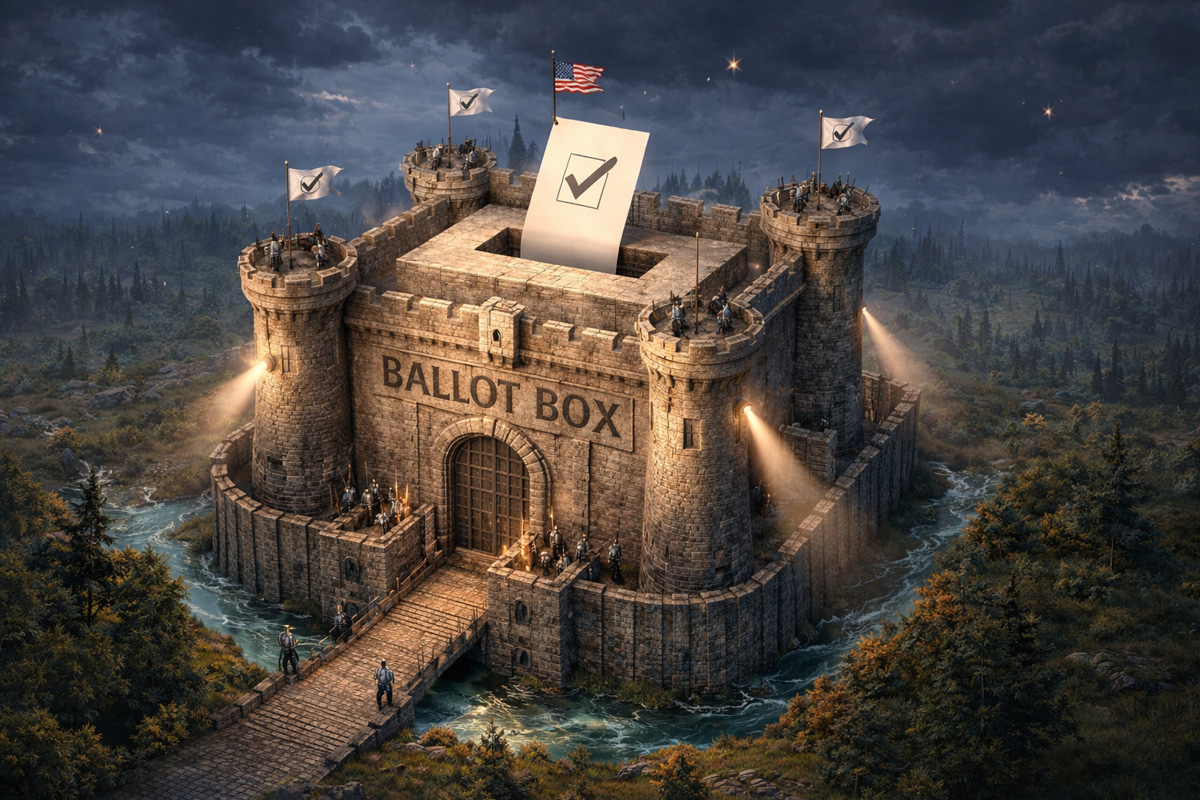
However some people fear that Trump and the Republicans will take steps to alter the process of the elections to their advantage. In this Op Ed we highlight possibility of tampering with the election process and what can be done to prevent it from happening.
According to the Constitution federal elections are the responsibility of the states.
Only Congress, and not the President, can make rules that affect the current election process. This means that each state has the ability to decide who can register to vote, what the voting process is, how votes can be counted and the outcome determined.
President Trump has said he wants to nationalize the election process but he has no legal ability to do that. Trump’s suggestion to nationalize elections in the United States goes against what the U.S. Constitution provides. Based on the text of Article 1, Section 4, Clause 1 the Constitution places the power to conduct elections – the times, places and manner of holding elections – clearly with each individual states. (See new USRESIST NEWS Civil Rights Policy Brief # 250 for more on this.)
Currently there also are several points of contention in the election process that worry political observers. These include:
-Voter Registration Requirements:
In most cases, you will need either a driver’s license or a state ID to register to vote. If you do not have either of these, you may be able to provide other types of documentation, including a bank statement or utility bill. But the required documents you need to register vary by state. Most states maintain a voter registration list that contains the names and contact information of those who have been registered in previous elections.
Many states have strengthened their voter ID requirements to help stop voter fraud. Examples of voter fraud occur when someone illegally casts a vote in the name of a dead person or someone who has moved. Voter fraud can be reported to state election officials or to the United States Department of Justice (DOJ). The Trump administration’s DOJ is likely to be on the lookout for any evidence of voter fraud, and use this as an excuse to invalidate election results.
Congress is trying to support a new dangerous voter registration law—the Safeguard American Voter Eligibility Act. This proposed Act would impose stringent new requirements to verify voter identity during registration, drastically curtail voting by mail, mandate automatic purges of voter rolls, and requite photo IDs at the polls.
-Creating and Maintaining a Voter Registration List:
Creating and maintaining an accurate voter registration list requires close monitoring and multiple checks and balances. These include keeping the registries up to date, eliminating duplicate registrations and voters who are no longer resident in that electoral district. Enforcement of anti-fraud and voter registration laws is also important. It deters future fraud as well as ensures that persons who have broken the law are held accountable for their actions.
– Absentee/Mail-In Voting:
Absentee and mail-in voting is voting that does not happen in person on Election Day but instead occurs another way—usually by mail. Absentee and mail-in ballots help widen the number of voters participating in an election. However some, especially right-wing supporters, want to limit or ban mail-in votes as they view them as ways to increase the votes from constituencies opposed to them.
-Poll Worker Training
At the same time, proponents of false claims of fraud in our election have attempted to recruit fellow election deniers to be poll workers. While state and local election officials cannot exclude poll workers based on their political beliefs, they can and should take reasonable steps to ensure that poll workers set aside any personal or partisan beliefs, follow the law, and faithfully carry out their duties.
-Election Security:
As cyber threats evolve, it is essential to assess the security of our election infrastructure regularly, to understand where new vulnerabilities may crop up. Congress should provide resources for state and federal agencies to conduct regular threat assessments and help state and local governments implement mitigation strategies to address the identified weaknesses.
-Election Monitoring
Scholars distinguish between types of election monitoring organizations in terms of quality. Some election monitors, often those with ties to authoritarian states, validate elections even when they are blatantly flawed. Monitors do not directly prevent electoral fraud, but rather record and report instances of suspicious practices. The monitoring may serve to disincentivize, prevent or minimize practices that undermine election quality, as well as election-related violence. Election observation increasingly looks at the entire electoral process over a long period of time, rather than at election-day proceedings only. The legitimacy of an election can be affected by the criticism of monitors, unless they are themselves seen as biased. President Trump has suggested he may use ICE officers to monitor polling place and election outcomes. This would be considered illegal unless they had the permission of local and state authoritiee; in which case they could only be stationed outside of polling places.
-Election Machine Reliability:
Elections present several opportunities for adversaries to compromise the electronic voting systems used by many states. However, despite evidence that such systems are vulnerable to a variety of attcks, there is little indication that voting through these systems has been altered in U.S. elections. Electronic voting machines currently in use by several states are known to have serious potential security vulnerabilities. One of the most important ways to secure electronic voting systems is to use election equipment thatcreates a paper record of every vote cast. Not every state currently requires the use of paper ballots, voter-verifiable paper records of votes, or permanent paper records for voting machines, but these safeguards are widely considered the most important security measures to protect against vote tampering. Paper records enable vote tallies to be audited and confirmed manually in the event of any suspected manipulation. Basic cybersecurity hygiene measures can also be important factors including securing voting equipment from physical tampering, installing software updates, disconnecting voting machines from the internet, and maintaining thorough logs of their use can further contribute to securing voting systems.
-Certifying Voter Outcomes
Election certification is an administrative task, usually done at the local and state level, that confirms the election process has concluded. At that stage, every vote has been counted and the results of the various races on the ballot have been determined. Simply put, certifying election results serves as an important “period” at the end of the postelection process “sentence.” Certification includes a series of deadlines at the local and state level that must be met before the results are officially finalized. Although it has proven to be unusual the certification process is another opportunity for fraudulent results to be posted by those doing the certification.